As part of deploying MCollective + ActiveMQ instead of my old Spread based system I need to figure out a multi location setup, the documentation says I’d possible so I thought I better get down and figure it out.
In my case I will have per-country ActiveMQ’s, I’ve had the same with Spread in the past and it’s proven reliable enough for my needs, each ActiveMQ will carry 30 or so nodes.
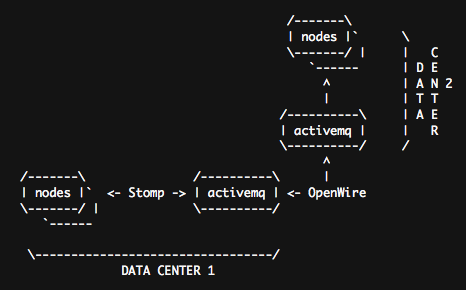
ActiveMQ Cluster
The above image shows a possible setup, you can go much more complex, you can do typical hub-and-spoke setups, a fully meshed setup or maybe have a local one in your NOC etc, ActiveMQ is clever enough not to create message loops or storms if you create loops so you can build lots of resilient routes.
ActiveMQ calls this a Network of Brokers and the minimal docs can be found here. They also have docs on using SSL for connections, you can encrypt the inter DC traffic using that.
I’ll show sample config below of the one ActiveMQ node, the other would be identical except for the IP of it’s partner. The sample uses authentication between links as I think you really should be using auth everywhere.
<broker xmlns="http://activemq.org/config/1.0" brokerName="your-host" useJmx="true" dataDirectory="${activemq.base}/data"> <transportConnectors> <transportConnector name="openwire" uri="tcp://0.0.0.0:6166"/> <transportConnector name="stomp" uri="stomp://0.0.0.0:6163"/> </transportConnectors> |
These are basically your listeners, we want to accept Stomp and OpenWire connections.
Now comes the connection to the other ActiveMQ server:
<networkConnectors> <networkConnector name="amq1-amq2" uri="static:(tcp://192.168.1.10:6166)" userName="amq" password="Afuphohxoh"/> </networkConnectors> |
This sets up a connection to the remote server at 192.168.1.10 using username amq and password Afuphohxoh. You can also designate failover and backup links, see the docs for samples. If you’re building lots of servers talking to each other you should give every link on every server a unique name. Here I called it amq1_amq2 for comms from a server called amq1 to amq2, this is a simple naming scheme that ensures things are unique.
Next up comes the Authentication and Authorization bits, this sets up the amq user and an mcollective user that can use the topic /topic/mcollective.*. More about ActiveMQ’s security model can be found here.
<plugins> <simpleAuthenticationPlugin> <users> <authenticationUser username="amq" password="Afuphohxoh" groups="admins,everyone"/> <authenticationUser username="mcollective" password="pI1jweRV" groups="mcollectiveusers,everyone"/> </users> </simpleAuthenticationPlugin> <authorizationPlugin> <map> <authorizationMap> <authorizationEntries> <authorizationEntry queue=">" write="admins" read="admins" admin="admins" /> <authorizationEntry topic=">" write="admins" read="admins" admin="admins" /> <authorizationEntry topic="mcollective.>" write="mcollectiveusers" read="mcollectiveusers" admin="mcollectiveusers" /> <authorizationEntry topic="ActiveMQ.Advisory.>" read="everyone,all" write="everyone,all" admin="everyone,all"/> </authorizationEntries> </authorizationMap> </map> </authorizationPlugin> </plugins> </broker> |
If you setup the other node with a setup connecting back to this one you will have bi-directional messages working correctly.
You can now connect your MCollective clients to either one of the servers and everything will work as if you had only one server. ActiveMQ servers will attempt reconnects regularly if the connection breaks.
You can also test using my generic stomp client that I posted in the past

